RED TEAM SUITE
Automated red-team testing
for your internet-facing surface
Continuously validate exposure, prioritize exploitable paths, and translate results into executive-ready reporting.
Invite-only beta. Zero-trust by design. ITAR registered + patented.
Already approved? Sign in to the beta.
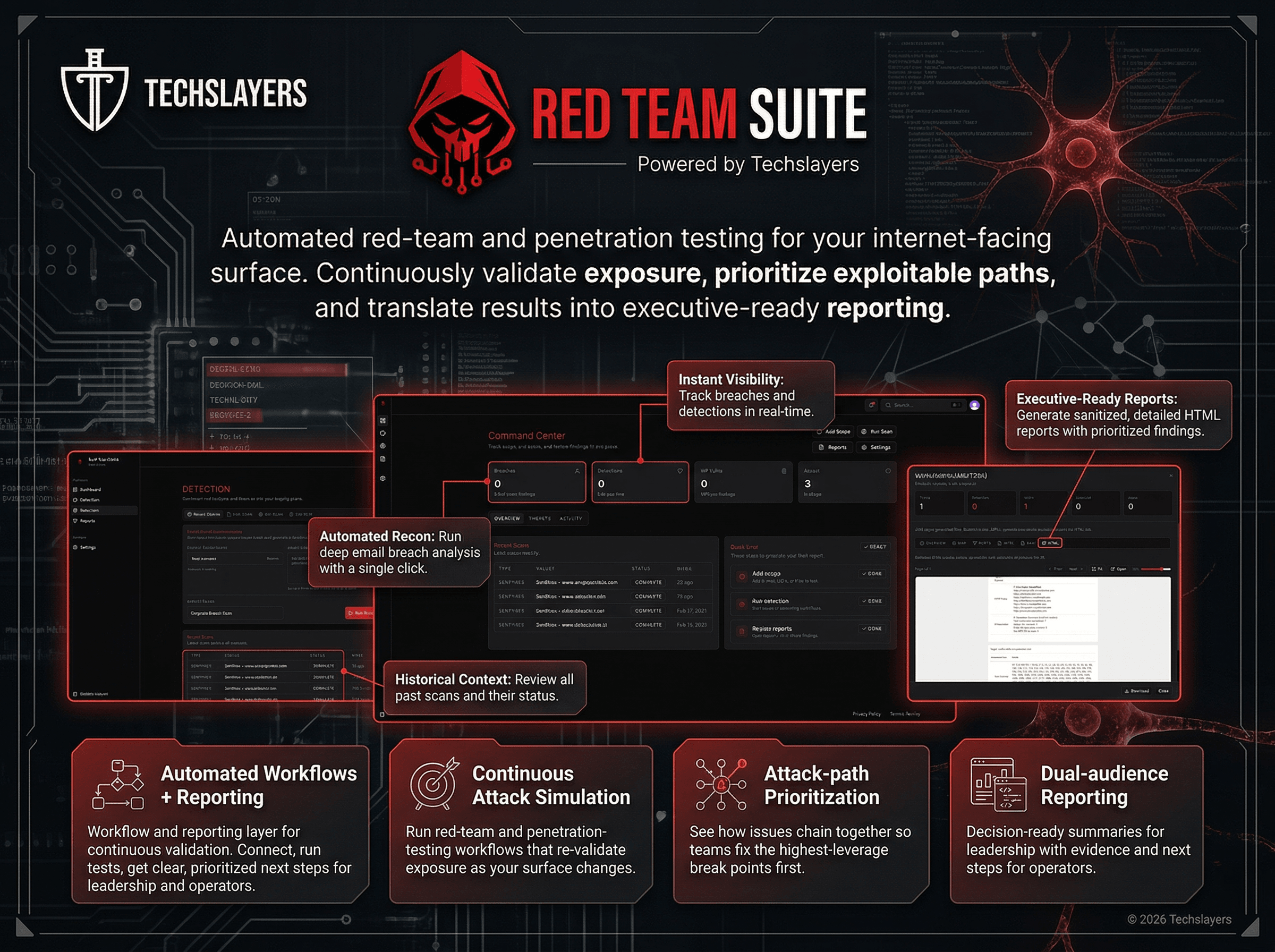
WHAT IT DOES
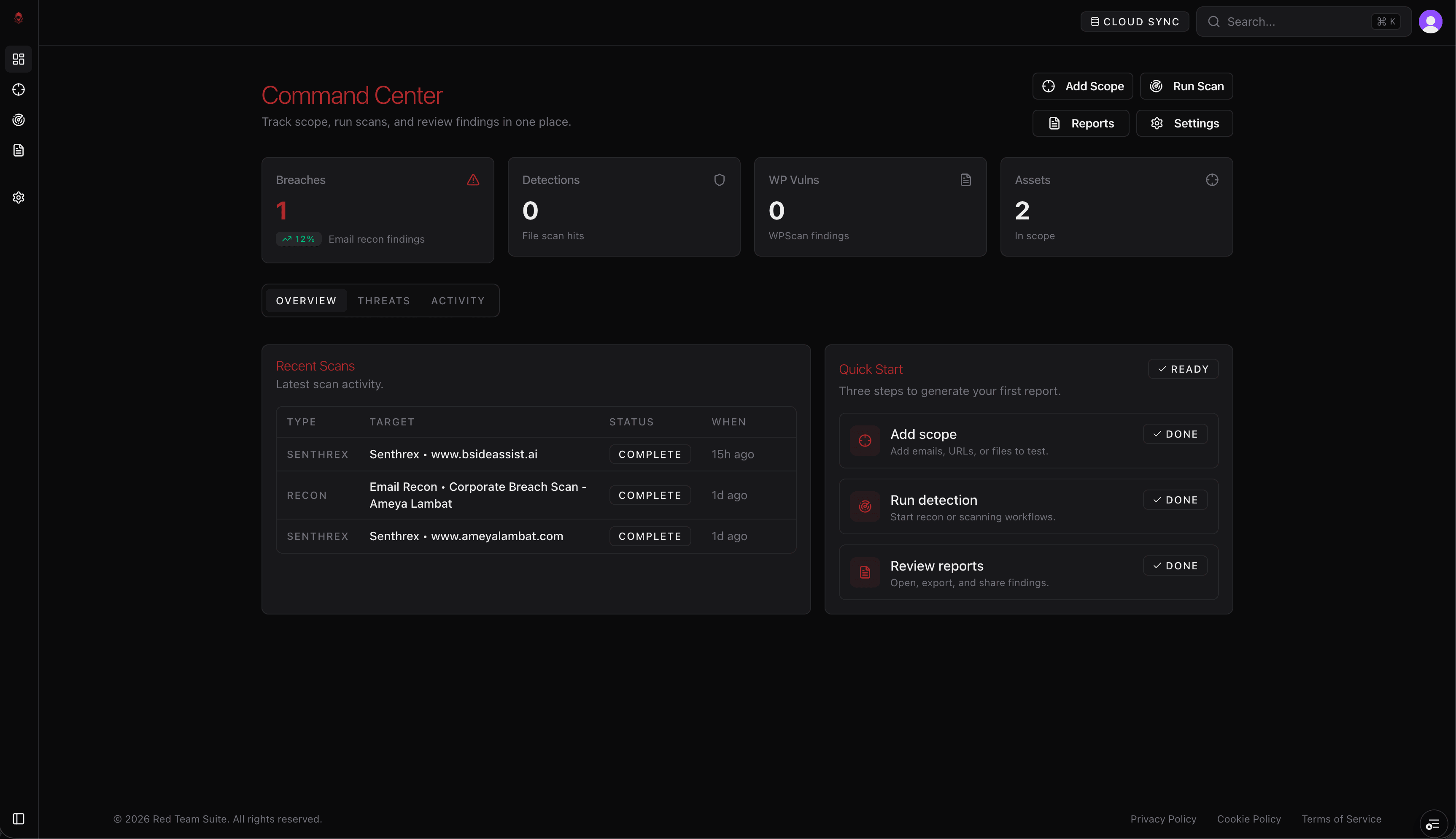
Automated workflows + reporting in one platform
Red Team Suite is a workflow and reporting layer for continuous validation. Connect your internet-facing surface, run automated tests, and get clear, prioritized next steps, with reporting for both leadership and operators.
Continuous attack simulation
Run red-team and penetration-testing workflows that re-validate exposure as your surface changes.
Attack-path prioritization
See how issues chain together so teams fix the highest-leverage break points first.
Dual-audience reporting
Decision-ready summaries for leadership with evidence and next steps for operators.
AT A GLANCE
At a glance
Who it's for
- Security leaders who need continuous validation across internet-facing assets
- Lean teams that want attack-path clarity without tool sprawl
- Leadership and operators who need one reporting layer and next steps
What problems it solves
- Point-in-time tests that go stale after every change
- Tool sprawl and disconnected findings with no ownership or workflow
- Reporting that doesn't translate cleanly from operators to leadership
Outputs / deliverables
- Automated validation with prioritized next steps
- Unified dashboards across exposure, assets, and coverage
- Dual-audience reporting: decision-ready for leadership, detailed for operators
ECOSYSTEM
TechSlayers tools, one platform
Access every TechSlayers product through Red Team Suite with shared dashboards and consistent reporting.
KEY CAPABILITIES
Key capabilities
A single platform that validates exposure and turns results into follow-through.
Scroll to explore →
Zero-trust by design. ITAR registered. Patented technology.
How it works
From waitlist to reporting in four steps.
What you get
Reporting built for decision-making and remediation. Leadership gets the narrative; technical teams get evidence and next steps.
- •Decision-ready summaries for leadership
- •Operator-level evidence and remediation guidance
- •Prioritized exposure and attack-path reporting
- •Follow-through reporting to track what changed
Frequently
asked
questions
LEARN MORE
Learn more
Explore practical guides and playbooks related to this topic.
Splunk Implementation for Lean SOC Teams: From First Log to Useful Alerts
A practical Splunk implementation guide for lean teams: data onboarding, alert design, triage ownership, and executive reporting that drives action.
Splunk vs Elastic vs Datadog vs Grafana: Which Security Stack Fits Your Team?
Use a practical decision framework to compare Splunk, Elastic, Datadog, and Grafana for security monitoring based on staffing, cost, and response goals.
Security Orchestration Platforms: A Practical Guide for Lean Teams
Learn what security orchestration is, how it differs from SIEM/SOAR, and a checklist to evaluate platforms that unify workflows and executive-ready reporting.
Executive-Ready Security Reporting: A Practical Template for Leadership
A practical template for executive-ready cybersecurity reporting: what leaders need, which metrics matter, and how to drive follow-through without drowning in dashboards.
CTEM and Continuous Security Validation: A Practical Playbook for Lean Teams
A practical guide to CTEM and continuous security validation: how to prioritize what matters, validate controls continuously, and report progress in a way leadership can use.
Shadow IT: The Hidden Security Risk Lurking in Your Network
Unknown devices and unauthorized cloud services create blind spots in your security. Learn how to discover shadow IT and why it poses a significant threat to organizations.
Join the invite-only beta
Get early access to Red Team Suite: automated workflows, unified dashboards, and reporting built for follow-through.
Already approved? Sign in to the beta.
What's included
- Automated red-team + penetration testing
- Unified dashboards + reporting
- Attack-path prioritization
- Dual-audience reporting (leadership + operators)
Delivery options
SaaS · Managed Service